Understanding that the promise of Smart Lighting cannot be realized without addressing the needs and requirements of Corporate IT teams Nimbus 9 has developed unifi Enterprise Edition.
Unifi Enterprise Edition serves the compliance and risk management mandate that governs Corporate IT by offering a suite of capabilities that address security, life-time control, integration, policy management, reporting & administration, support and more.
.
SECURITY
IDENTITY AND ACCESS MANAGEMENT
Nimbus 9 understands that in this day and age it is of paramount importance for Enterprises to securely manage digital identities. Nimbus 9 has developed key Identity and Access Management capabilities within the the Unifi platform.
Not only is the unifi platform capable of handling in a stand alone capacity Identity and Access Management, the unifi platform is architected to seamlessly integrate into our Enterprise customers’ IAM business process, policies and technologies. Corporate InfoSec and IT teams can control user access and usage of the unifi Platform in the same manner in which they control access to all other critical enterprise systems, applications and data.

MULTI-FACTOR AUTHENTICATION
unifi Enterprise Edition allows for customers to implement 2 factor authentication whereby a user is not only required to provide their password to access the platform but also an expiring code sent to the user by SMS.
Requiring a second form of identification, SMS-2FA decreases the probability that an attacker can impersonate a user and gain access the unifi platform. Once a user’s identity is authenticated unifi allows for the use of several of the most common authorization protocols that verify what capabilities and information the user is authorized to access in accordance with corporate information security guidelines.
PROTOCOLS, FRAMEWORKS & DIRECTORY SERVICES
End-to-end Encryption
The Unifi Platform is secured through end-to-end Encryption. Cryptographic protocols are used for communication between all wired and wireless system components. Each individual component in the Unifi platform is secure as an autonomous entity but also secure in it’s interactions with the other entities existing on the platform.
DEVICE TO DEVICE
Wireless traffic between the Gateway and individual light fixtures, sensors, switches, etc. is encrypted using 128 Bit AES Encryption. The 128 Bit Advanced Encryption Standard(AES) provides a never before broken standard which would take emerging Quantum Computers 6 months to exhaust all the possibilities of a 128-bit AES key. Breaking the 128-bit AES Cipher would also require onsite presence. Finally, by design, devices on the Unifi Platform retain little data themselves making any attempted hack meaningless. Through the combination of 128-bit AES and 256-bit SSL encryption all communication on the Unifi Platform is fully encrypted and secure end-to-end.
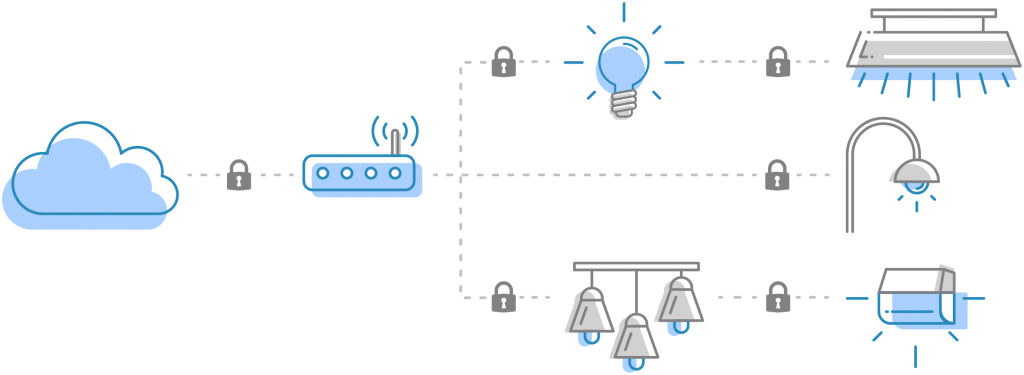
DEVICE TO CLOUD
While wireless intra-device communication uses 128-bit AES encryption, communication between the Gateway and the Cloud is secured through 256-bit Secure Socket Layer(SSL) encryption. Secure Socket Layer is a type of encryption based on data “tunneling” where the Gateway and Cloud initiate an encrypted communication channel through the negotiation of encryption methods. When connecting to Cloud through SSL, the Gateway requests an authentication certificate. Once the certificate is verified, both computers negotiate an encryption method and then the Gateway sends an encryption/decryption key to Cloud. Once the session is established all communications during the session will be encrypted using the agreed-upon technique. SSl is highly secure and used most frequently for communications with banks and credit agencies to maintain the privacy and security of customers.
Gateway Security
GATEWAY INTROVERSION
Another key security feature tied to Nimbus 9 provided hardware is Gateway Introversion. This means the Gateway, the hardware device that establishes and maintains the wireless network, is by by default, in a closed state. When the Gateway is in an introverted state no new devices, even if they are speaking the same protocol, can join the wireless mesh network. Any network join requests from any device that are sent when the Gateway is in introversion mode will be ignored. The only thing that can bring the gateway out of introverted mode and allow it to accept new devices joining the local wireless mesh is a Commissioning command sent from Cloud.

ACCESS CONTROL LIST
Complementing Gateway Introversion, the Unifi Cloud maintains an Access Control List for every gateway on a customer site. The Access Control List is essentially a whitelist of known devices that are authorized to be on a gateway’s network. During the commissioning process, the Gateway is put into extroverted mode meaning it can accept specified devices onto the network. When a device joins the network, it’s MAC address, the device’s unique identifier is sent to Cloud to be added to the Access Control List.
The only time devices can join the wireless mesh network is when Cloud enters the gateway into extroverted mode with a commissioning command. Once the gateway finds the new devices it communicates all of the unique Device IDs to the Cloud. At this point Cloud writes these new Unique Device IDs to the gateway’s ACL. Now every device on the local wireless mesh network is registered with the Access Control List maintained by Cloud.
ACL is extremely important as it maintains a list authorized devices on the gateway’s wireless network. A gateway cannot autonomously add devices to the Mesh network. It must receive authorization from Cloud to add devices. This prevents one of the most common malicious attacks known as “Spoofing”. Even if a device’s unique ID was captured, system security wouldn’t be compromised as the “spoofing” device would be ignored since the compromised ID already exists on the ACL so any network join requests would be ignored as the ID would be known to be a duplicate.

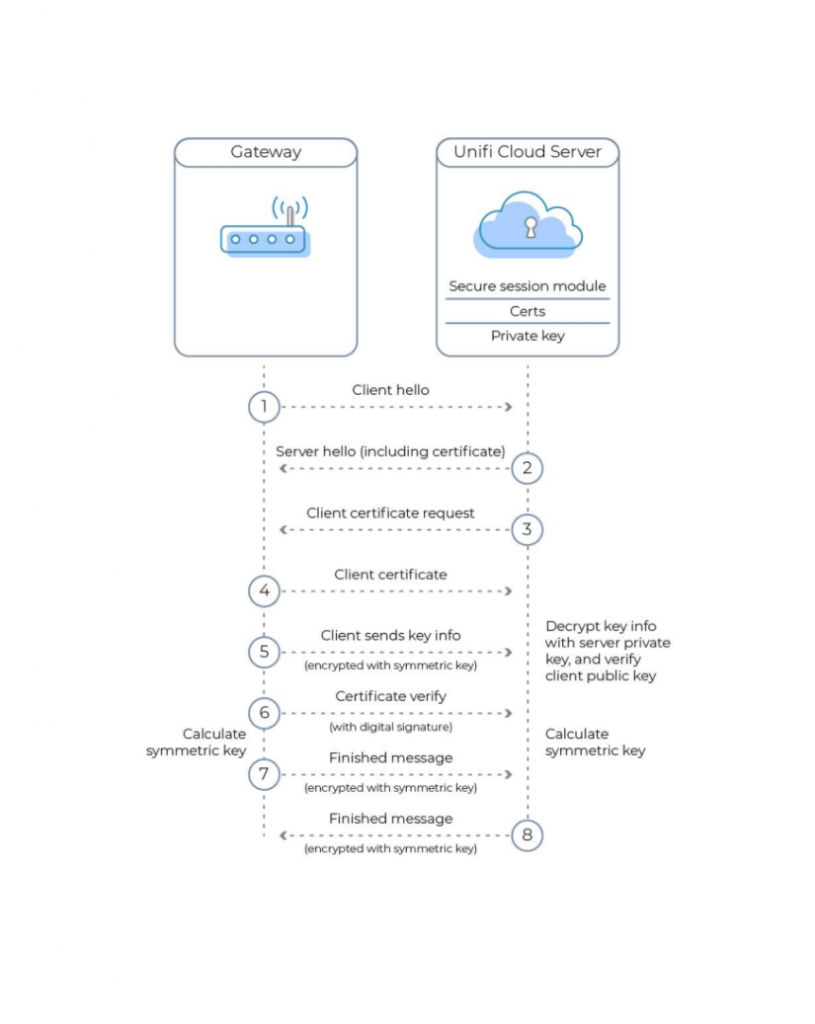
MUTUAL TLS AUTHENTICATION
Nimbus 9 Gateways are secured using Mutual TLS (mTLS) authentication. mTLS authentication ensures that traffic is both secure and trusted in both directions between a Gateway and Nimbus 9’s Cloud. mTLS allows requests that do not log in with an identity provider (e.g. IoT devices) to demonstrate that they can reach a given resource. Client certificate authentication is also a second layer of security for team members who both log in with an identity provider (IdP) and present a valid client certificate.
With a root Certificate Authority (CA) in place, Unifi only allows requests from devices with a corresponding client certificate. When a request reaches the application, Unifi responds with a request for the client to present a certificate. If the device fails to present the certificate, the request is not allowed to proceed. If the client does have a certificate, Unifi completes a key exchange to verify and authenticate.
In those instances where an Enterprise Customer is running Unifi on their own servers then said customer will serve as the Certificate Authority thereby using their own InfoSec infrastructure.
ARCHITECTURE

CONFIGURABLE CLOUD DEPLOYMENT
While the unifi Enterprise Cloud offers unrivaled security, redundancy and scalability that is capable of serving the needs of the overwhelming percentage of customer requirements there are instances when a customer simply cannot use a public cloud solution. The portable composition of the unifi™ Cloud’s architecture means that In-Region Cloud, Hybrid Cloud, Private Cloud and “air-gapped” deployment options are available and fully supported by Nimbus 9.

CLOUD BACKUP
Unifi Enterprise Edition customers have the option to sign up for Cloud Backup Service offered by Nimbus 9. The unifi Cloud Backup Service leverages the capabilities offered by Amazon Web Services allowing customers to replicate their unifi instances in different Availability Zones.
While Availability Zones are engineered to be isolated from failures in other Availability Zones customers can opt for further resiliency by backing up their unifi instances in different AWS regions.
EEPROM VIRTUALIZATION
While unifi Cloud Backup is designed to address failure and recovery specific to the unifi application Nimbus 9 has also developed an essential recovery capability should a local gateway fail. The local gateway is the hardware device responsible for creating and maintaining the wireless mesh network. Critical information about the wireless mesh network is stored in the gateway’s Electrically Erasable Programmable Read-Only Memory (EEPROM).
Unifi Enterprise Edition periodically virtualizes the EEPROM and stores in Cloud a copy of the EEPROM. Virtualization ensures that in the event that a gateway ever failed completely a new gateway could be installed and the “virtualized EEPROM” could be pushed down to the new replacement gateway. This capability eliminates the “single point of failure” concern about gateways. Additionally it means that hardware failures can be resolved without any recommissioning or reprogramming of the system allowing for a “gateway hotswap”. This gateway hotswap feature is some of the unique intellectual property that Nimbus 9 has developed for the unifi platform.

REPLICATION SERVICES
unifi Enterprise Edition addresses the question of Ownership & Control through our Replication Services offering. Customers have several Replication options which can be as simple as locally replicating data and analytics captured by the unifi platform for backup purposes only to running all control capabilities on local infrastructure.
- Data Replication
- Configuration Replication
- MicroService Replication
- Control Replication
- Full Site Replication
While the emergence of cloud computing delivers significant value to Corporate IT teams it presents several risks and challenges most importantly loss of control. Corporate IT teams are ultimately responsible for the security, reliability, availability and recoverability of business applications whether they run in-house or are Cloud delivered. The advent of IoT and Smart Infrastructure has further amplified the challenge around control for Corporate IT teams.
Enterprise Editions Replication Services ensure that Corporate IT teams are always in control.
DEVELOPER TOOLS
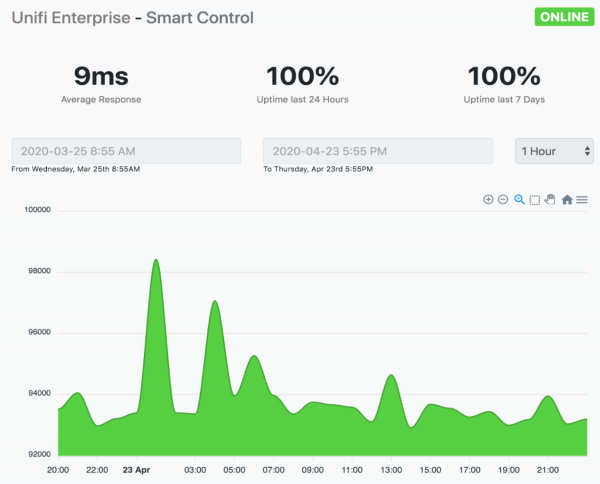
UPTIME & PERFORMANCE MONITORING
The Nimbus 9 Status site provides unified real-time status and forward-looking maintenance information for all of Nimbus 9’s web applications and services. Nimbus 9 customers can use the site to check status a glance or access detailed incident and maintenance information. Customers can also subscribe to receive emails about incidents and maintenance events.
Performance Degradation and Service Disruption incidents that appear on the site impact multiple customers and must be at least 5 minutes in length. The site will provide regular updates until the incident is resolved.
The site, https://status.nimbus9.io/ not only summaries of uptime percentages over the last 24 hour and 7 days but also the average response from the specific applications or endpoints. Data can be sorted by date and hour to provide not only a “moment in time” snapshot of system performance but sortable historical data to better understand system performance over time.
Nimbus 9 Status is the truest reflection of our company’s ethos: a company that is committed to their customers’ success and willing to accept total transparency in the validation of that commitment. Nimbus 9 is certain that we have engineered the best Smart Building platform on the market and are the only platform provider willing to prove it.
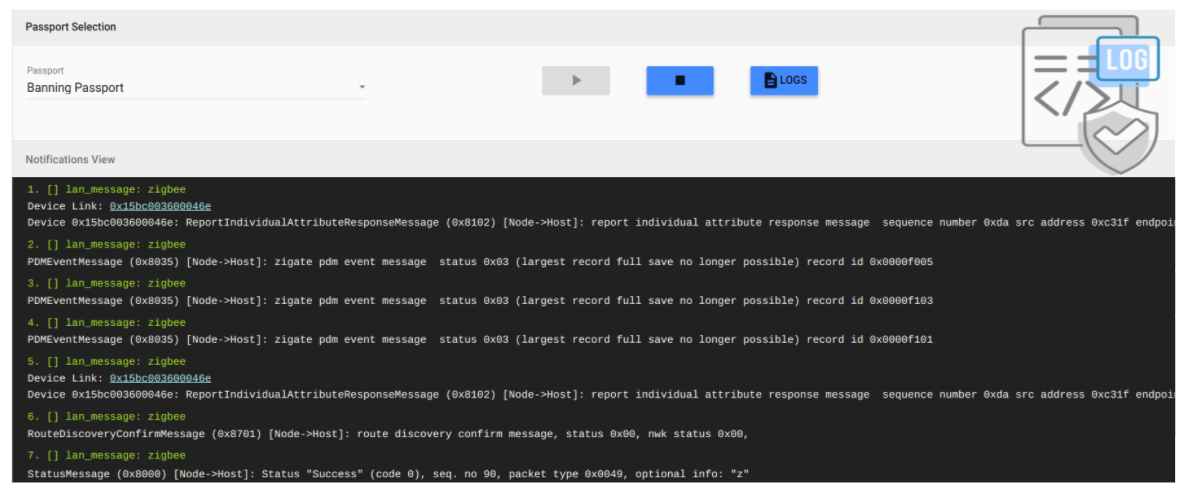
LOGGING
The ability to generate logs has been a “must have” feature in enterprise applications for a while. The ability to forward those logs to a central log server has taken center stage as requirement for Corporate IT teams.
With Enterprise Edition Log files are time-stamped, and may record practically anything that is happening behind the scenes on the unifi platform. Audit logs, transaction logs, event logs, error logs, message logs are some of the different log files the unifi platform captures.
In addition to operational and system performance logs unifi Enterprise Edition allows the logging of Identity & Access data. Every single login action on the unifi platform can be recorded and stored in the database and reviewed in the Admin Console. Furthermore all administrative actions from user creation to role assignment can also be recorded and reviewed.
unifi Enterprise Edition even allows Corporate IT teams to integrate unifi logs with their organization’s log management solution.

PUBLISHED APIs
From inception unifi Enterprise edition’s developmental focus has been creating a platform upon which Smart Building applications can be quickly developed and deployed. While Nimbus 9 has developed essential Smart Building applications in house we understand that large enterprises need to integrate these N9 applications into other Corporate systems and applications. The unifi Platform with it’s microservices architecture puts the API front and center enabling seamless integration of existing applications and the development of new applications that extend the value of a customer’s investment in unifi Enterprise edition.
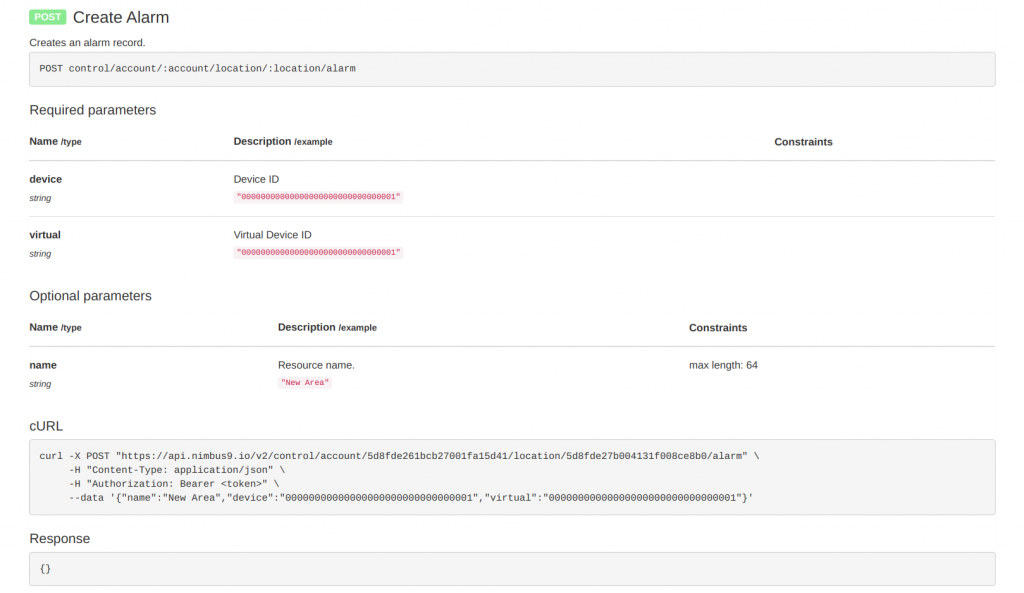
DOCUMENTATION
Nimbus 9 understands how important it is to provide developers with code documents associated with source code (which includes README and API documentation) that are thorough and complete. The entire Nimbus 9 code base from firmware to web applications and APIs is documented and available to developers.
Nimbus 9’s documentation keeps track of all aspects of the unifi platform. Documentation assists development, code maintenance and knowledge transfer to both internal and third party developers.
Documentations goal is to make information easily accessible, provide a limited number of user entry points, help new users learn quickly, simplify the product and help cut support costs

DECOMMISSIONING TOOLS
Should a Nimbus 9 customer elect to not renew their Annual Subscription for the unifi Cloud Platform or on-premise services said customer has a couple of options from a continuity perspective. The customer can choose to just run the system through Independent Local Control without any of the higher level unifi Platform Cloud Services and without customer support. Additionally a customer may elect to decommission the Nimbus 9 system and use another provider.
The decommissioning process would reset all hardware to the factory state so that a new controls provider could be implemented. All the tools necessary to successfully decommission the Nimbus 9 system are provided to a customer’s administrators.






